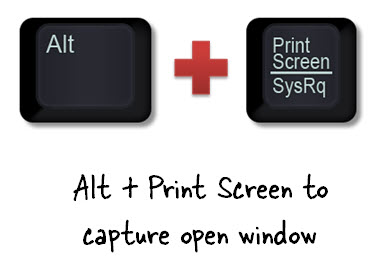
ALT PRNT Screen Practice is Becoming Less Defensible When It Comes to Discovery;
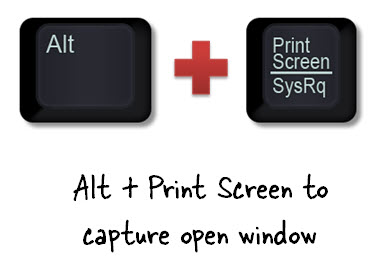
There is no argument that social media discovery is becoming more and more prevalent in litigation discovery and discovery related requests. In the past, a simple print screen of a website or LinkedIn profile page converted to a pdf or a printout was an acceptable form for production. Today, social media evidence is becoming more and more scrutinized and the authentication standards for social media data collections are becoming the same standards as any other ESI authentication process. By not following best practices when it comes to social media data collections there is a significant risk of having key evidence in support of a client’s case disallowed by the court. Think this is some hippy dippy bologna? Well-there is case law now to prove it.
A Massachusetts Appellate Court Commonwealth v. Banas, 2014 recently ruled a Facebook post submitted by the prosecution in a criminal case to be inadmissible as evidence. What happened was the State introduced a screenshot of a Facebook post without any authenticity or metadata of the post. The court ended up citing “evidence that . . . originates from an e-mail or a social networking Web site such as Facebook or MySpace that bears the defendant’s name is not sufficient alone to authenticate the electronic communication as having been authored or sent by the defendant.”Another case United States vs. Vayner, 2014 involved the US Federal Appellate Court, Second Circuit, who overturned a criminal conviction for improper authentication upon finding that the lower court mistakenly admitted a screenshot of the defendant’s alleged profile on VK.com. Essentially “the lower court jury convicted the defendant on a single count of the unlawful transfer of a false identification document. The government’s key evidence included a screen shot alleging the defendants VK.com profile page.” The lower court admitted the printout however, the appellate court determined that the government presented insufficient evidence that the page was what the government claimed it to be—that is, the defendants profile page.
Don’t Go Overboard-Social Media Requests Should Not Be Overly Broad:
At the same time with social media, it is a rarity to have complete and unfettered access to a person or entities as an example Facebook or LinkedIn account. An eDiscovery Daily article explained in the case of Howell v. The Buckeye Ranch the defendant asked the plaintiff to disclose all user names and passwords for each of the social media platforms in question. The case involved sexual harassment allegations related to employment discrimination.
The defendant wanted to prove, through social media-based evidence, that the plaintiff was in fact living a joyous life, though the judge deemed the request as “unduly burdensome and overbroad.” Judge Abel ruled, “The fact that the information defendants seek is in an electronic file as opposed to a file cabinet does not give them the right to rummage through the entire file.” “The same rules that govern the discovery of information in hard copy documents apply to electronic files. Defendants are free to serve interrogatories and document requests that seek information from the accounts that is relevant to the claims and defenses in this lawsuit. Plaintiff’s counsel can then access the private sections of Howell’s social media accounts and provide the information and documents responsive to the discovery requests.” In short, the Magistrate Judge Mark Abel ruled that the social media discovery request overboard.
The first step with any ediscovery related matter is to get the experts involved early. Make sure you have a really good understanding of the entities IT infrastructure including all types of social media involved. Also realize there are a number of forensic tools available on the market specifically for social media discovery that you should make sure to ask your service provider about and to ensure that best practices are followed when collecting potentially responsive data.
References
